
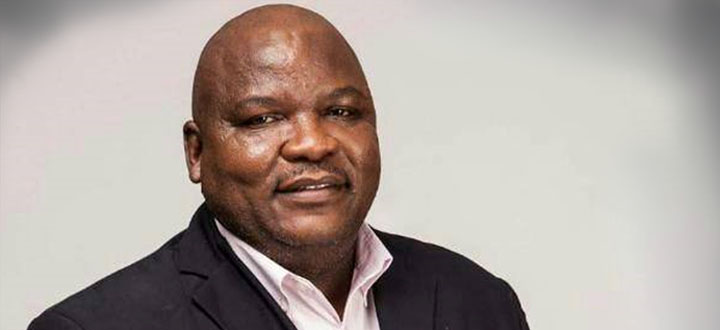
Ozias Ncube Senior Lecture: Supply Chain Management, Member of the Alumni Association Executive Committee
Introduction
Supply chain design has assumed significant importance recently because of vulnerability of supply chains. In particular, complex supply chains are susceptible and hence vulnerable to various disruptions. Although some disruptions occur infrequently, it is imperative that their profile be examined, so as to understand the extent of impact on supply chain performance, with at-times disastrous consequences for the different supply chain players. This article will attempt to present a brief insight on latest developments on supply chain vulnerability, trends regarding dominant vulnerabilities and provide some suggestions on how to profile disruptions that may cause realisation of these vulnerabilities.
Developments and trends
Complexity in supply chain arises depending on a number of elements. It can either be due to: (1) global supply chains – implying either global supply, global distribution networks and or global markets. This creates multiple points of contact within the chain, with particular “ at risk” view to logistical challenges, cultural changes, global financial systems and appropriate legal and legislative frameworks applicable to manage supply chain relations. (2) technology – in particular the desire for integration and collaboration. However, the extent of the development and adoption of technology and appropriate management systems to complement the integration objective is rarely homogenous throughout the chain. There are pockets of excellence and some players are always lagging behind. This disturbs information flow and affects supply chain visibility. (3) Innovation – in particular with respect to adoption of cloud enabled capabilities, utilization of drone and related technology of the 4th Industrial Revolution (4IR) Era, for example. However, these tend to draw labor force resistance as sub-Saharan Africa, as “developmental states” lean more towards labour-intensive supply chain operations. (4) knowledge and skills gap – with a significant number of multi-national entities’ supply chain headed by either non-nationals and or non-Africans, this appears to be a huge exposure with many of the sub-Saharan Governments displaying nationalistic tendencies and not renewing expatriates permits beyond the initial 3 – 5 year periods.
It is clear that (1) is unavoidable. This is a growing trend in supply chain as organisations seek cheaper supplies and growing markets. The focus may probably be about streamlining and re-orienting the supply chain to be lean and responsive. (2) and (3) above present both opportunities and huge vulnerabilities. With regards to opportunities, 4IR creates space and platforms to leap-frog forward by modernizing utilisation of supply chain resources while effectively dealing with stakeholder concerns around sustainability – societal and environmental impacts. Cloud-enabled technologies provide wider capability, and maximises opportunities for supply chain visibility without worrying abound bandwidth constraints and other related soft “constraints”. However, while the benefits are clear, it is the corresponding cyber-security scare that is of much concern, hence the classification as a vulnerability. Of-late, there has been a marked increase on cyber security attacks in the supply chains, mostly focused on changing contractual terms, hijacking and re-routing of delivery, changing of product characteristics and flagrant flouting of customs and excise duty procedures. There has been instances where supply chain entities are locked-out of their systems for ransom payments before access is granted. This definitely requires a closer look and appropriate mitigation be determined.
With regards to the knowledge and skills gap, I believe knowledge transfer mechanisms are in place, personal development plans for the identified personnel have been (or need to be) put in place for accelerated development in-line with each country’s skills development legislation. Liaising with supply chain professional bodies, accredited training service providers, and recognised education programs does provide an out-of-company solution that is credible.
Impacts and Managerial Considerations
However, in general, it is important to identify what may cause realisation of these vulnerabilities so as to put measures in place for mitigation to ensure resilience. Many analysts use different tools and methodologies. For this discussion, I have chosen to discuss a methodology derived from H. PECK (Resilience Centre, Department of Defence Management and Security Analysis, Cranfield University). The approach views vulnerability and resilience from 4-parameter perspective: (i) risk sources; (ii) consequences of risk sources; (iii) risk drivers that turn risks into consequences; (iv) strategies that address the risks
In this case, vulnerability is understood to be the exposure to serious disturbance arising from risks within the supply chain and risk being losses associated with undesirable outcomes. It is important to be able to identify and characterise the disruptions that may cause realisation of vulnerability. In this case disruption is considered to be any outcome of a process whereby one or more events (referred to as “triggering event”) taking place at one point in the supply chain adversely affect the performance of one or more components located elsewhere in the supply chain. The factors of policies to be used to determine reaction (mitigation) to ensure resilience may be grouped as follows: (a) information related policies; (b) buffer related policies; (c) alternate sourcing policy and (d) Component substitution. The suitability of the approach will be influenced by the supply chain’s realities. Whichever approach is chosen, it has to be monitored with regards to its strategic impact on the following goals: (a) lead time; (b) cost; (c) quality, and (d) flexibility. Organisations can add other indicators that are also reflective of their reality over and above these baseline four.
In my opinion, if this can be done, then it is safe to say the organisation has sufficient capability to cope with vulnerability and ensure resilience.
Publish date: 2019-05-27 00:00:00.0
Contact the Marketing and Communication office: Ms Thami Kaunda at kaundn@unisa.ac.za
011 652 0339
Telephone: +27 11 652 0248 / +27 11 652 0291
Email: sbl@unisa.ac.za
Physical Address:
Cnr Janadel and Alexandra Avenues
Midrand, 1686
Gauteng, South Africa
Download map & directions (PDF)